DATA SECURITY OWNERS
MANAGE YOUR DATA SECURITY POSTURE ACROSS ALL CLOUDS AND DATA PLATFORMS
Problem statement:
In the cloud, data is much more easily sourced and shared, but I lack visibility into the resulting data security risks and issues.
Solution:
Quickly analyze and visualize, in a single dashboard, access patterns and user behavior to uncover hidden risk caused by ineffective controls, forgotten data, and overly permissioned access.
- Dark data
- Ghost accounts
- Overprivileged accounts
- Suspicious activity

Problem statement:
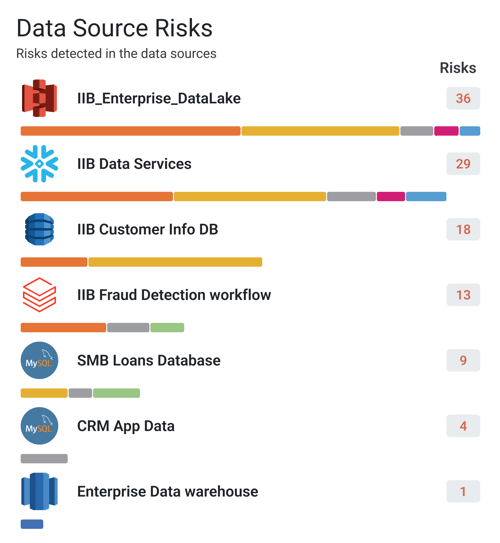
Understanding my data security posture and proving compliance is hard when data is distributed across multiple clouds and platforms, each with their own data security tools and capabilities.
Solution:
Visualize your data security posture and demonstrate compliance with GDPR, HIPAA, PCI, SOX, and other regulations across all your disparate cloud data stores with a single dashboard and set of reports.
- Quantify how much of your risk is coming from a lack of regulatory compliance
- Drill down into compliance risks by each data source
- Detailed breakouts of what’s driving compliance risk
- Directly click through to remediation actions right from each violation alert
Problem statement:
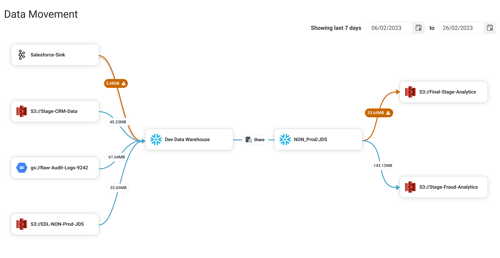
Data is continually being onboarded and shared with new users, and I lack the ability to detect new data security risks in real-time.
Solution:
Track your data as it proliferates across disparate clouds and platforms, and get alerted for suspicious behavior and indicators of exfiltration, as it occurs.
- Top-down view of data proliferation across clouds
- Real-time alerts on suspicious data movement
- Visualize data flow from source to destination, even across clouds
- Take instant action from each alert to contain risk before it becomes an incident
Problem statement:
As data complexity and usage increases, it gets harder and harder to determine the right actions to remediate risks without slowing down the business.
Solution:
Instantly take corrective action on risk-based alerts with contextual prompts and recommendations based on the type of alert.
- Risk-based alerts across all instances of disparate data clouds
- Alerts categorized by Compliance, Exfiltration, Shadow IT, and other risk areas
- Drill down into risk categories and further down into specific data sources and alerts
- Contextual menus empower you to take corrective action immediately, based on the type of alert and risk

SEE FOR YOURSELF HOW WE CAN HELP YOU
