Data Owners: Be Your Organization’s Data Hero.
Get the Right Data to the Right People, Instantly and Securely, Everytime
Problem statement:
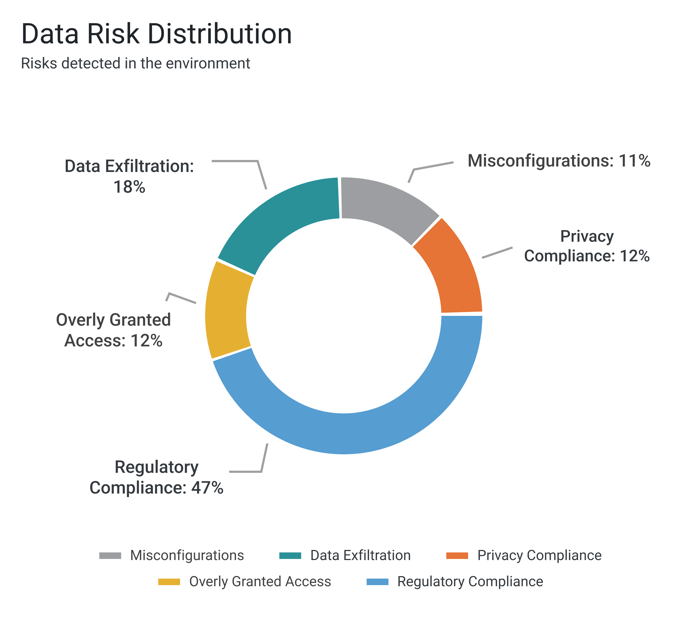
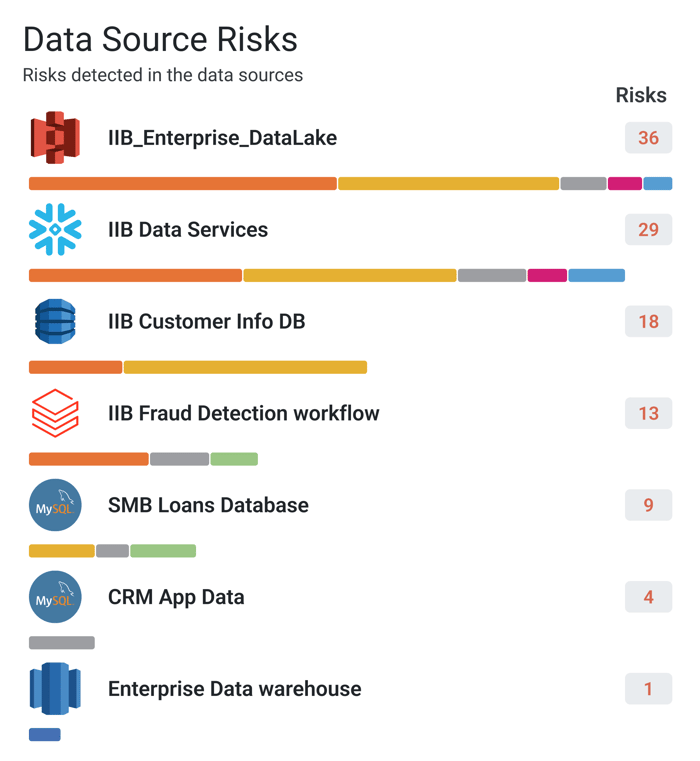
In the cloud, data is shared and distributed to more and more data consumers, so it is hard for me to maintain up-to-date visibility of all data access and usage.
Solution:
Easily connect TrustLogix to your Snowflake and other data stores, and quickly get visibility to how and by whom your sensitive data assets are being accessed.
- Identify overprivileged accounts
- Observe data usage pattern
- Single view of all roles and privileges
- Identify “dark data”, sensitive data not being used at all
SEE FOR YOURSELF HOW
Problem statement:
In the cloud, hand-coded or data-silo-specific data access tools slow me down, and I can’t keep up with the volume and complexity of data consumers’ data access requests.
Solution:
Define and deploy granular policies from a business-friendly console instead of getting entangled in the complexities of SQL code and cloud- and platform-specific security constructs.
- Implement and update policies at the speed of business
- Integration with IAM and Governance platforms puts their roles and tags at your fingertips as you design your policies
- Incorporate your own permission and entitlement tables into your policies
- Guarantee consistent policy enforcement across instances and disparate data clouds
Problem statement:
Data consumers need access to do their jobs, yet regulatory and corporate privacy policies mandate that certain attributes must be de-identified. How can I deliver exactly the right data to the right people, so they get the data they need while still complying with policies?
Solution:
Define precise access policies down to the specific rows and columns that are truly needed using RBAC, ABAC, and Data Entitlements for your various data consumers.
- Define de-identification and access policies at the role and attribute level
- Discover and associate columns and rows with sensitive data attributes, and deploy attribute-level policies everywhere that data appears
- Associate access policies with roles according to least-privilege principles

Problem statement:
It is hard for me to keep up with the ever-increasing volume and urgency of incoming requests for data access, without slowing down the business
Solution:
You’ve put in the effort to define Least Privilege policies for data consumers across your organization. TrustLogix empowers you to apply them quickly and uniformly to onboard new LOBs and apps in just minutes while ensuring that you’re sticking to your own best practices and compliance policies.
- Create and apply policy templates that can be applied across multiple data sources and sets of roles
- Ensure standard sets of privileges are applied regardless of where the data resides

Problem statement:
I need to share a dataset with a business partner, using features such as Snowflake’s data sharing. But there are sensitive data attributes that must be properly redacted before sharing with another organization, and regulations such as GDPR require this. How can I do this consistently across all my data sources?
Solution:
In addition to the right access control policies, these attributes should also be masked or otherwise de-identified. TrustLogix lets you specify de-identification policies and associate them with your sensitive data attributes, ensuring your business partner can access relevant data while also complying with regulations.
- Discover over-privileged accounts and unauthorized access
- Identify sensitive data attributes requiring redaction
- Audit and alert on data sharing compliance issues and risks

Problem statement:
Troubleshooting data access issues is difficult and labor-intensive for me, and meanwhile my data users don't have the data they need to do their jobs.
Solution:
Keep your users productive by quickly troubleshooting access issues using visualization tools to navigate your role hierarchies and inherited entitlements.
- Visualize role and privilege hierarchies for a given data set and identify what data is accessible for a given role and privilege
- Quickly update and deploy a revised policy or role to address the issue
.png?width=1000&height=452&name=Certify4x%20(1).png)
SEE FOR YOURSELF HOW WE CAN HELP YOU

