How the TrustLogix Platform Simplifies Data Security in Snowflake
Stay in the Know
Subscribe to Our Blog
Author: Srikanth Sallaka, Co-Founder and Head of Product at TrustLogix
Date: November 3, 2021
TrustLogix has worked closely with the Snowflake team on this integration architecture. We'd like to acknowledge Paul Gancz, Partner Solutions Architect at Snowflake for his valuable contributions to this blog.
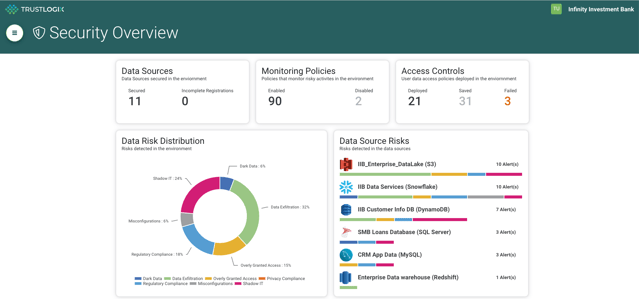
As the speed at which data is generated continues to increase, businesses rely on multiple data platforms to process, store, and analyze data. This explosion of data leads to siloed data security and operations, which in turn is creating a nightmare for data owners, data security operations, and governance teams. At TrustLogix, we believe that securing data at the source will empower business users and organizations with greater control over their data, and deliver actionable insights while streamlining data security and privacy operations. As a Snowflake Data Cloud partner, the TrustLogix platform strategy is to lead with data usage monitoring, identify security blind spots, and then enable data teams with access control policies to secure data within Snowflake, data pipelines, data lakes, and BI analytics platforms.
Given the ease of adding data to the Snowflake Data Cloud, and the desire to make that data available to as many users in an organization as possible, securing the data through standard policies and controls is obviously important, and is a key piece of the TrustLogix solution. Equally important is the need to identify and control attempts to access data in ways that, while technically allowed, could potentially violate security policies. The combination of policy definition and enforcement, along with monitoring and automated detection of improper data access, provides the security and privacy controls that organizations require.
TrustLogix Monitoring & Access Service for Snowflake uses a patent pending cloud-native technology, called a Trustlet, to monitor and secure data in the Snowflake data cloud. With this solution, data engineers, security teams, and governance teams can monitor and secure access to data. The TrustLogix solution provides the following key capabilities:
- Observe and learn any mis-use of data
- Automate enforcement of granular access controls
- Cloud-native Trustlet architecture
TrustLogix Leverages Snowflake Java UDF and Snowpark Preview Features to Deliver Advanced Data-Security-as-a-Service Capabilities in the Snowflake Data Cloud
Snowflake has recently announced many new features, including Snowpark and Java User Defined Functions (UDFs). These new features deliver more control to data owners and consumers to process data without moving data out of the Snowflake cloud. We are excited to use these features, allowing us to deliver advanced security use cases such as building risk scores and preventing Separation of Duties (SoD) and Sarbanes-Oxley (SOX) compliance violations in real time.
Automated Detection of Separation of Duties Violations
As many organizations move to cloud-based data platforms they need to establish a framework for managing regulatory and compliance requirements. SOD is a basic building block to minimize any fraudulent or non-compliant behavior. In an organization that uses Snowflake for managing their accounting data, a person responsible for building analytics reports on Journal entries should not be the same person who is also responsible for loading this data into the system. Similarly in organizations that use Data warehouses to improve product offerings by analyzing customer usage patterns, GDPR mandates that individuals responsible for designing and implementing security must not be the same person as the person responsible for testing security or conducting security audits.
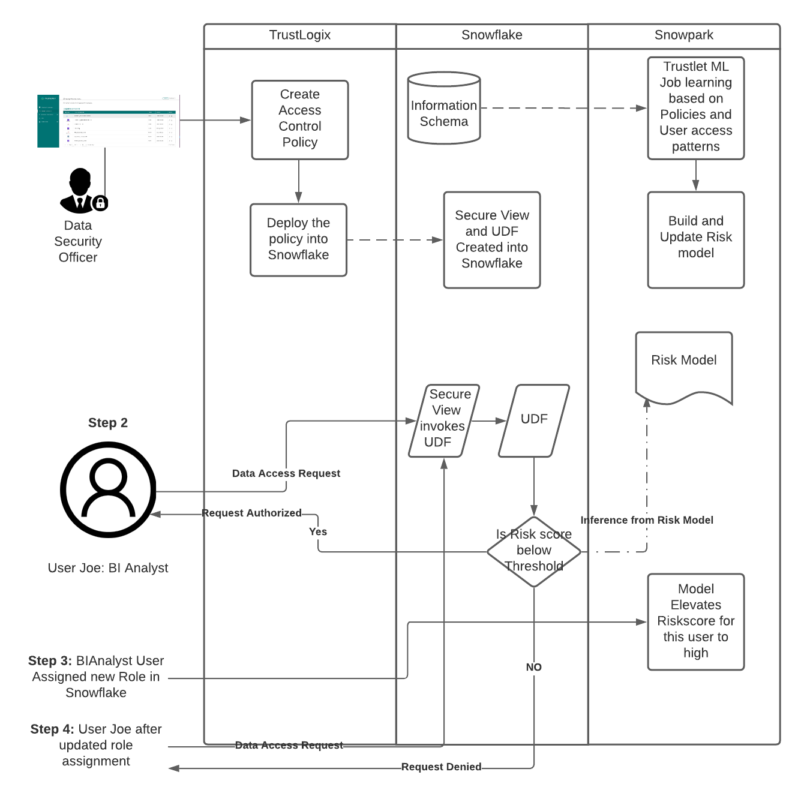
Trustlogix’ patent pending risk-based access control model will continuously monitor for SOD and SOX compliance violations and help achieve the required business compliance. We use ML Models to build a risk score to identify conflicts in privilege and role assignments. We are leveraging Snowpark to implement these models. We use Snowpark dataframes in the implementation to get the latest roles, privileges, policies, and access data from the Snowflake Information Schema to build the model and implement a risk score. We use this risk score in a secure view to block any data access requests by users who use the conflicting role and stop risky actions before they occur.
The sequence diagram below illustrates the steps on how TrustLogix enforces risk based access controls to ensure complaint usage of data. Users will access the data in Snowflake via a secure view created by TrustLogix. This view has a built-in UDF to compare the risk score for this data request. The request is approved or denied based on the acceptable threshold of the risk score.
Here is a video which demonstrates automated detection of SoD violations using the Snowpark and Java UDF features:
With the TrustLogix solution, data engineers, data governance, and data security officers can get visibility into data mis-use, discover data access and sharing patterns, and enforce access control policies with an easy to use policy console and scalable cloud-native Trustlet architecture.
Contact us at hello@trustlogix.io to schedule a demo.
Please visit Product Page to learn more.
You can also download our Snowflake Product Overview to read about the benefits of our Snowflake product integration.
